Table of Contents
The future landed 10 years ago, and with it an innumerable number of devices, technologies, methodologies, and trends has come with it to stay. Some studies foresee that by 2020 there will be 200 billion connected things. We are talking of course, about the era of IoT (internet of things). The IoT describes a model where every device and tool that can be used is connected with each other through “the cloud”, and thus is possible to track, create and store data. Because of that reason, everything (car, fridge, TV, console, smartphone…) can be hacked, anybody can get in, take that information and use it with bad manners. The discipline that works to prevent this is called Cybersecurity. And today we will look at main cybersecurity threats, facts, statistics, examples and tips.
Cybersecurity is all those technologies, processes and controls designed to protect systems, networks and data from Cyber Attacks, which are considered any damage or unauthorized access to data, and the latest exploitation from it.
The importance and transcendence that cybersecurity has in every current government is obvious, right? Imagine how many messages we send every day to our friends, family, business, people that we meet.. Now, multiply it by number of people doing it in the world, the result is monstrous. Scale that to the amount of data that is created in only one week, two, a month!
Internet knows more from us than we think, did it ever happen to you, checking your flight to New York one evening and then, the day after you wake up and go to Facebook or you read daily news and there are offers popping up with flights to New York, Hotels in New York, etc. All that is due to the information and your preferences stored online, and it is called Big Data.
Sensitive information, intellectual property, financial data, military plans….all this information information should be well protected. Because if it hacked, only God knows how people can use it against people, companies, governments, etc.
However, even though we live in the most connected and digital era of all times, people are not really aware of the consequences of not taking care of the cybersecurity threats.
There are 3 main cybersecurity issues:
1- Lack of understanding and knowledge. We all know what to do when we want to buy a new T-shirt online. But we don’t know how many things we accept/agree on to be able to do that. In this process of purchasing clothes, before the last click that confirms we bought something, there are thousands of agreements, cookies, open browsers, insecure pages, etc. We agree because we don´t understand it, or we are in a hurry and we don’t really pay attention to these things, so rather than read it and understand the basis of security, we just agree on everything to buy our stuff as fast as possible.
2- New and different technologies. The industry is growing very rapidly, and faster than we can imagine. By the time we start only understanding the basics of a new cutting-edge technology, other companies, launch new methods and applications that allow cyber attackers to use it for their benefit. Hackers are usually people interested in new technologies and they are fully aware of the new trends and approaches in the digital industry.
3- Lack of time and money. Related to the previous points, because of the few security knowledge people have, they use a popular argument: “sorry, we don’t have time/money for that”. But sometimes it is worth to take some time on understanding the basics of the world we live in today, because if not, hackers get easily in the systems that use basic protection. Just imagine the cost for the e-commerce company if hackers get the payment information of the clients, this cost can be a bankruptcy of a company and courts for many years. That’s why all banks in the world are trying to work with the best and the most secure systems to protect their clients from the robbers.
These issues can lead to a breach in the system. Let’s look at the main damages:
Main cyber attacks’ consequences
1- Reputational damage. Losing money is not the worst thing that can happen to a company. When you lose trust of customers and stakeholders, and when you fail to protect the privacy of your customers, this is the hardest thing to recover. You will have to prove again that they can trust you, and that is not an easy task.
2- Theft. This part is related to copyright and competitive advantage. As mentioned before, not all cyber attacks search for financial benefits, most of them are in pursuit of any type of advantage with the competitors, being it a confidential information, secret formulas, etc.
3- Financial Loses. It can be a financial lose that can actually kill you or a financial lose that makes you slow down, allowing your competitors to move faster.
4- Fines and courts.This upcoming 28 of May there will be launched a new law protecting the customers and its privacy. It will be mandatory to have a strong and rigid legislation of data and digital information. The fee is a 20 million € or the 4% of the global annual revenues.
Any many more, let’s look at some cybersecurity threats and attacks examples:
Cyber attacks examples
According to Forbes, hacking software is becoming more sufficient, increasing the impact that hackers can have on a business. Cyber hackers are becoming more sophisticated agendas such as espionage, disinformation, market manipulation and disruption of infrastructure, on top of previous threats such as data theft, extortion and vandalism.
Hardly a week goes by without the announcement of some major breach. It’s gotten so that many attacks don’t even get reported any more unless they are especially spectacular. Did you hear about the autumn Taiwanese bank compromise that resulted in US$60 million being stolen? Huge amount of money, but this news were not even shown on some news TV channels.
Let’s look at famous examples of companies, that went almost bankrupt because of cyber attacks: TalkTalk, from UK, where a cyber attack cost 400.000 pounds in losses, or the more than known Sony hacking scandal, actually there is a movie about it.
UCLA, for example, reported a potential breach of 30,000 student records when a hacker broke into a server containing students’ personal data this year.
Last year, at Michigan State University, someone breached a database of approximately 400,000 records containing names, social security numbers, MSU identification numbers and other important personal information; the university determined that 449 records had been accessed before authorities were able to take the files offline just 24 hours after the incident occurred.
In 2017, when the IRS discovered a data breach involving its IRS Data Retrieval Tool, it revealed that as many as 100,000 taxpayers may have had their personal information compromised. In the IRS incident alone, the agency suspects that nearly 8,000 fraudulent returns were processed, resulting in a loss of approximately $30 million.
These are just few examples, if attackers were able to hack these companies, imagine with down-the-street ones.
You may track the cyber attacks here.
The process of being digitally secure can be a “pain in the ass”, however, it is a process that, just like we´ve seen make sense to invest in to avoid bigger headaches in the future.
Alarming Cybersecurity threats: facts and stats
- There is a hackers attack every 39 seconds
- 43 percent of cyber attacks target small business. 64% of companies have experienced web-based attacks. 62% experienced phishing & social engineering attacks. 59% of companies experienced malicious code and botnets and 51% experienced denial of service attacks.
- The US government spends $13 billion per year on cybersecurity threats but warns that cyber-attacks continue to evolve at a rapid pace.
- Right now, In Australia, 80% of CEOs rate cybersecurity threats as a top investment priority and place it amongst the top five risk areas for their business, according to the latest KPMG CEO Outlook survey.
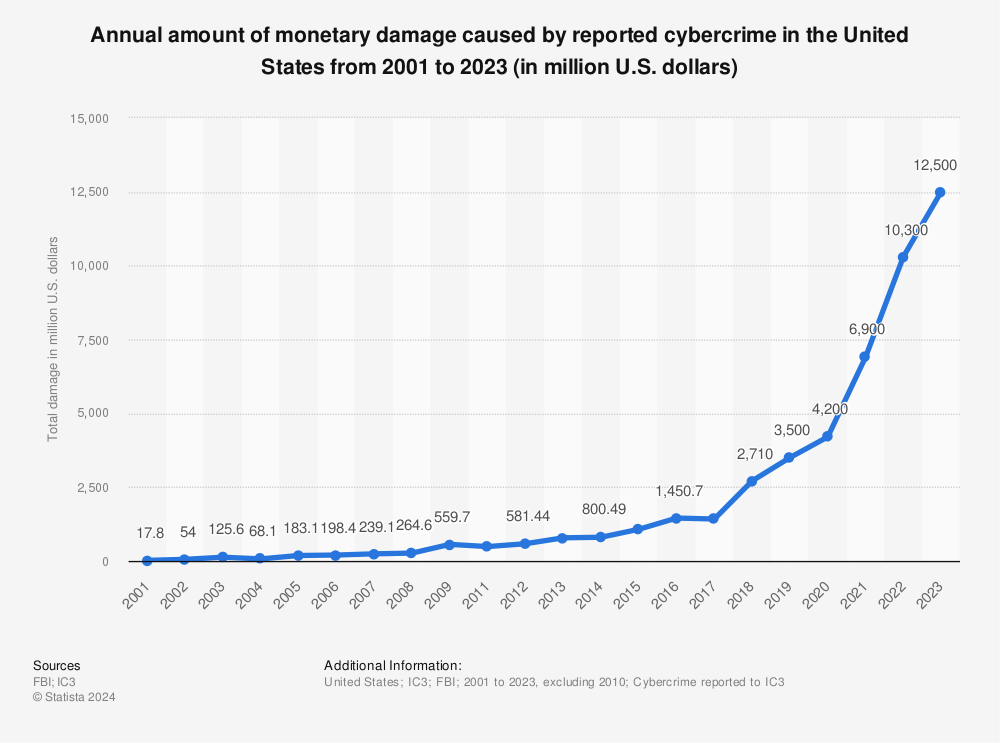
- Cyber crime damage costs to hit $6 trillion annually by 2021. As the frequency – and costs – of cyber-insecurity grows, spending on cybersecurity threats defense grows too, spending which is expected to reach some $90 billion in 2018.
- 1 in 131 emails contain a malware.
- Unfilled cyber security jobs is expected to reach 3.5 million by 2021 — compared to about 1 million in 2016.
- In 2017, 6.5 percent of people are victims of identity fraud — resulting in fraudsters defrauding people of about $16 billion
- China is the country with highest number of malware-infected computers in the world.
- It takes most business about 197 days to detect a breach on their network.
- 81 percent of data breach victims do not have a system in place to self-detect data breaches.
- 95 percent of Americans are concerned about how companies use their data.
- In Telstra’s recent Cyber Security report, data shows that 59% of Asian organizations experienced a business-interrupting security breach at least once a month.
- Average annual amount of cybersecurity incidents – 90 million
Cybersecurity threats: examples of attacks
Malware
One of the most popular ones. If you’ve ever seen an antivirus alert pop up on your screen, or if you’ve mistakenly clicked a malicious email attachment, then you understand what it is.
Once malware is in your computer, it can wreak all sorts of havoc, from taking control of your machine, to monitoring your actions and keystrokes, to silently sending all sorts of confidential data from your computer or network to the attacker’s home base.
Attackers use a variety of methods to get malware into your computer, but at some stage it often requires the user to take an action to install the malware. So,this can include clicking a link to download a file, or opening an attachment that may look harmless, etc.
Phishing
When an attacker wants you to install malware or divulge sensitive information, they often turn to phishing tactics, or pretending to be someone or something else to get you to take an action you normally wouldn’t. In a phishing attack, an attacker may send you an email that appears to be from someone you trust, like your boss or a company you do business with. The email will seem legitimate, and it will have some urgency to it. In the email, there will be an attachment to open or a link to click. Upon opening the malicious attachment, you’ll thereby install malware in your computer. If you click the link, it may send you to a legitimate-looking website that asks for you to log in to access an important file.
SQL Injection Attack
SQL stands for structured query language; it’s a programming language used to communicate with databases. Many of the servers that store critical data for websites and services use SQL to manage the data in their databases. A SQL injection attack specifically targets this kind of server, using malicious code to get the server to divulge information it normally wouldn’t. This is especially problematic if the server stores private customer information from the website, such as credit card numbers, usernames and passwords, etc.
Cross-Site Scripting
In an SQL injection attack, an attacker goes after a vulnerable website to target its stored data, such as user credentials or sensitive financial data. But if the attacker would rather directly target a website’s users, they may opt for a cross-site scripting attack. Similar to an SQL injection attack, this attack also involves injecting malicious code into a website, but in this case the website itself is not being attacked. Instead, the malicious code the attacker has injected only runs in the user’s browser when they visit the attacked website, and it goes after the visitor directly, not the website. One of the most common ways an attacker can deploy a cross-site scripting attack is by injecting malicious code into a comment or a script that could automatically run.
Denial of Service
If you flood a website with more traffic than it was built to handle, you’ll overload the website’s server and it’ll be nigh-impossible for the website to serve up its content to visitors who are trying to access it. This can happen for innocuous reasons of course, say if a massive news story breaks and a newspaper’s website gets overloaded with traffic from people trying to find out more. But often, this kind of traffic overload is malicious, as an attacker floods a website with an overwhelming amount of traffic to essentially shut its cybersecurity down for all users.
Session Hijacking
When you’re on the internet, your computer has a lot of small back-and-forth transactions with servers around the world letting them know who you are and requesting specific websites or services. In return, if everything goes as it should, the web servers should respond to your request by giving you the information you’re accessing. This process, or session, happens whether you are simply browsing or when you are logging into a website with your username and password. The session between your computer and the remote web server is given a unique session ID, which should stay private between the two parties; however, an attacker can hijack the cybersecurity by capturing the session ID and posing as the computer making a request, allowing them to log in as an unsuspecting user and gain access to unauthorized information on the web server.
Credential Reuse
Users today have so many logins and passwords to remember that it’s tempting to reuse credentials to make life easier. Even though cybersecurity best practices universally recommend that you have unique passwords for all your applications and websites, many people still reuse their passwords. Once attackers have a collection of usernames and passwords from a breached website or service, they know that if they use these same credentials on other websites there’s a chance they’ll be able to log in. No matter how tempting it may be to reuse credentials for your email, bank account, and your favorite sports forum, it’s possible that one day the forum will get hacked, giving an attacker easy access to your email and bank account. When it comes to credentials, variety is essential.
Social media threats
Cybersecurity threats are popular among corporates as well, hackers love exploiting corporate social media accounts for the embarrassment factor to glean passwords that might be shared between the social media site and the corporate network. Many of today’s worst hacks started out as simple social media hacking. Don’t underestimate the potential.
This is just a selection of common cybersecurity threats and cyber attack types, there are more, but these ones are the most frequent ones, the ones you can check, remember and improve in order not to be hacked by these techniques.
If you like this article about cybersecurity threats, you may like:
-
- Terrifying Cyber Crime Statistics
- Mixed reality – Pushing out into the new world
- Virtual reality technology: main trends, statistics & startups
- Barcelona; one of the best smart cities in Europe
- Elastic search: advantages, case studies & books
- Human-centered innovation: careers, benefits & examples
- Natural language processing projects & startups to watch
- Barcelona makes it to the top 5 of innovation hubs
- Top smart city projects & leaders to watch
- Disruptive technology & innovations to track
- Digital health hub
- The 6 Types Of Cyber Attacks To Protect Against In 2018
If you are interested in cybersecurity threats or other quality software related topics, I highly recommend you to subscribe to our monthly newsletter.